GANA Payment, a project on BNB Smart Chain, lost over $3.1 million after an attacker took control of key contractual rights, reports have revealed.
The thief carried out much of the transport via Tornado Cash on BSC and Ethereum, while around $1 million remains unused on Ethereum addresses.
How the attack took place
According to posts by blockchain researcher ZachXBT, the exploiter consolidated the stolen assets at the address 0x2e8***5c38 before sending 1,140 BNB – approximately $1.04 million – into Tornado Cash on BSC.
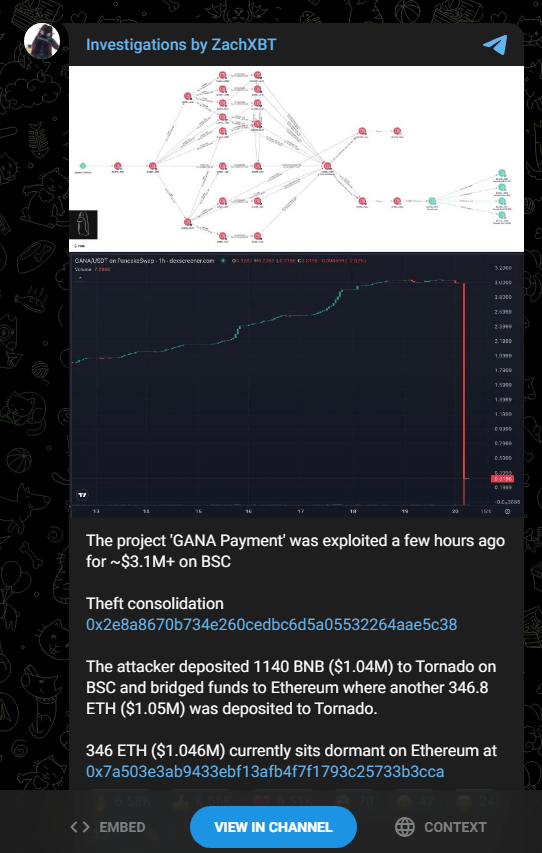
The thief then transferred the funds to Ethereum and transferred 346.8 ETH worth approximately $1.05 million through the same mixer.
According to Zach (@zachxbt), the GANA Payment project was mined for over $3.1 million on BSC earlier today.
The attacker first sent 1,140 $BNB ($1.04 million) in Tornado Cash on BSC, then linked the stolen funds to #Ethereum and deposited 346 others $ETH ($1.05 million) in Tornado.
THE… pic.twitter.com/q7DL8Mdpzf
– Onchain Lens (@OnchainLens) November 20, 2025
Around 346 ETH, or almost $1.05 million at the time, remains untouched at the address 0x7a503***b3cca. According to reports from security firm HashDit, the breach began when the ownership of a GANA contract was changed without authorization, giving the attacker administrator-level control over the staking logic.
Urgent announcement from GANA
The GANA Interaction Contract was targeted by an external attack, resulting in unauthorized asset theft. Our technical team, in collaboration with an independent third-party security company, launched an emergency investigation to analyze the attack vector,…
– GANA Payment (@GANA_PayFi) November 20, 2025
HashDit’s analysis shows that whoever takes control could call deactivation routines and force the system to release many more GANA tokens than it should have.
These excess tokens were quickly sold for more liquid assets and then funneled to privacy tools. It’s a familiar script: manipulate permissions, create or mine tokens, convert them to stable or liquid crypto, then launder.
Who spotted it and what happened next
ZachXBT reported the suspicious movements on his Telegram channel. HashDit then dug into the contract and identified the ownership change as the trigger.
The GANA team issued an emergency notice acknowledging unauthorized activity on their interaction contract and said they had retained an external security firm to investigate.
The project said it would map user addresses and permissions as part of a planned reboot and publish recovery steps and timelines through official channels.
🚨HashDit Alert🚨
HashDit monitored this @GANA_PayFi was compromised for approximately $3.1 million $GANA.
Users should NOT trade with the $GANA token for now, and wait for the team announcement!
The funds were deposited in TC:
Fundamental cause: property of… pic.twitter.com/XZzuoMmf8D
-HashDit | now with Pro Extension (@HashDit) November 20, 2025
Featured image from Pexels, chart from TradingView

Editorial process as Bitcoinist focuses on providing thoroughly researched, accurate and unbiased content. We follow strict sourcing standards and every page undergoes careful review by our team of top technology experts and seasoned editors. This process ensures the integrity, relevance and value of our content to our readers.