Google Threat Analysis Group (TAG) has identified “Coruna,” a sophisticated iPhone crypto exploit kit that migrated from state-sponsored espionage to mass financial theft targeting wallets. The toolkit, which exploits a staggering 23 vulnerabilities in iOS versions 13.0 to 17.2.1, is currently being deployed by cybercriminals to harvest BIP39 seed phrases from iPhone users visiting compromised gaming sites and fake exchange sites. This represents a significant escalation of mobile threats, effectively placing military-grade surveillance tools in the hands of thieves looking to drain MetaMask and managed wallets.
This discovery reveals a worrying trend where high-end exploits, once reserved for intelligence agencies, are being repurposed for broader criminal activities. Apple fixed the specific vulnerabilities exploited by this kit in iOS 17.3 and later, but the large number of devices running outdated software creates a lucrative target. Users visiting these “watering hole” sites are vulnerable to immediate compromise without any interaction.
A few weeks ago, Apple announced that “iPhones and iPads (are) approved to manage *classified* NATO information” 😂
It turns out that even the most modest cybercriminals were using 0days to hack Apple devices 🙂
-Patrick Wardle (@patrickwardle) March 3, 2026
EXPLORE: Three Solana Rigs Shut Down Following $27 Million Exploit
The iPhone Crypto Exploit: How Coruna Kit Targets iPhone Users
The mechanics of the Coruna exploit reveal a level of engineering typically reserved for state actors, not financial fraudsters. Potential victims are lured to malicious websites masquerading as legitimate services, often fake versions of the WEEX exchange or obscure gambling portals, where a hidden JavaScript framework fingerprints the visitor’s device. If the script detects a vulnerable iPhone model, it silently delivers a WebKit remote code execution (RCE) payload, bypassing Apple’s Pointer Authentication Code (PAC) protections to gain system-level access.
Once inside the device, the malware doesn’t care about ransomware tactics; he goes straight to get the keys to the safe. The kit launches a file system scan, specifically looking for data associated with popular self-custody applications, performing a highly targeted seed phrase theft operation. It searches for cached QR code images, unencrypted notes containing backup chains, and specific application data containers for wallets such as MetaMask and BitKeep. The stolen data involves the exfiltration of 12-24 word BIP39 mnemonic phrases that grant full control over a user’s funds, which are then transmitted to command and control servers via encrypted channels.
It should be noted that this process takes place entirely in the background. The exploit chain includes sophisticated mitigation workarounds that allow it to operate without crashing the browser or alerting the user, making it particularly deadly for investors who manage high-value portfolios on mobile devices. The Coruna toolkit also uses unique obfuscation techniques to hide its traffic, making it more difficult to detect by standard mobile security filters.
EXPLORE: Shiba Inu Team Issues Critical Scam Alert on Fake SOU Recovery
The timeline: what Google TAG found
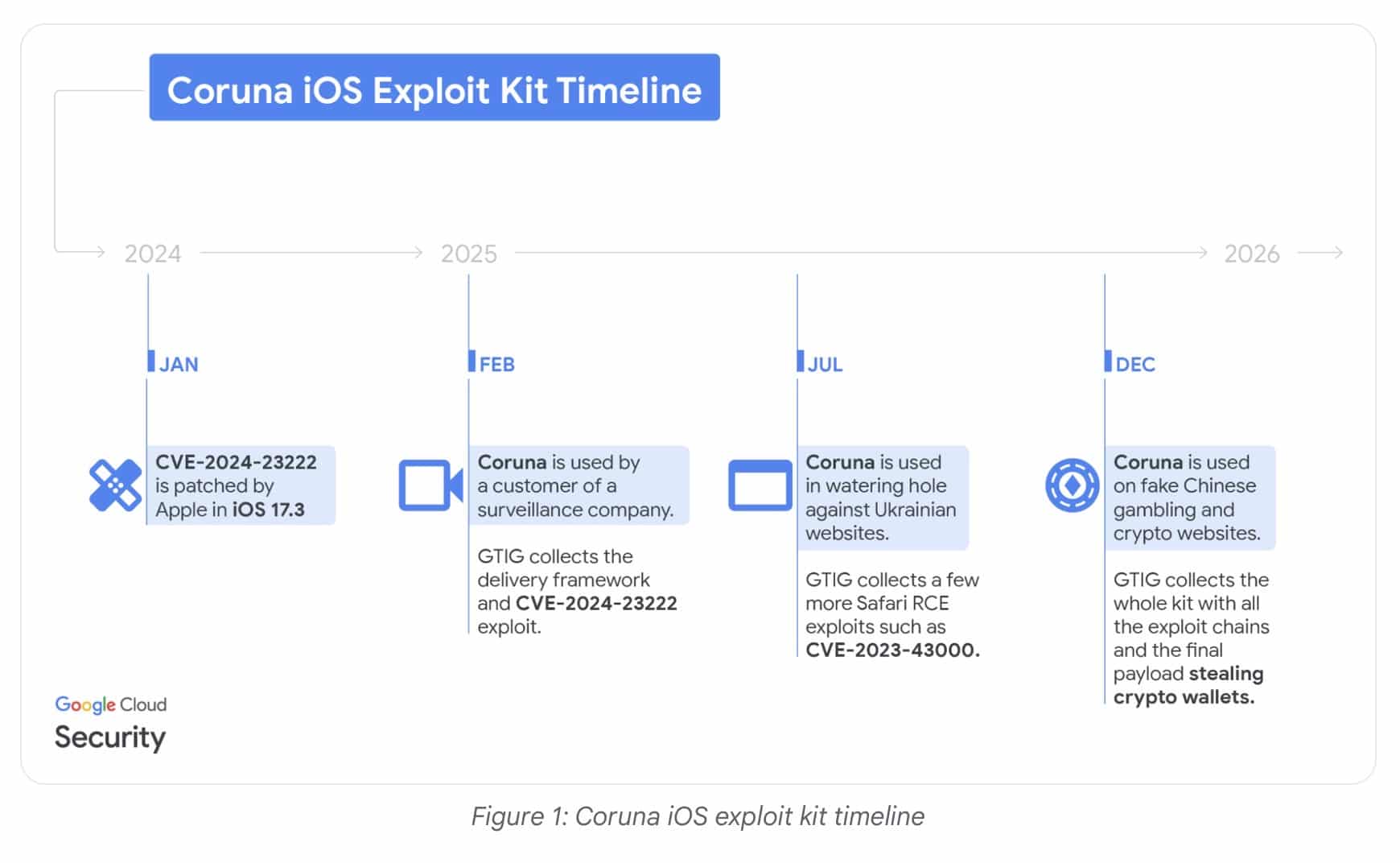
Coruna iOS Exploit Timeline Source: Could Google
The Google TAG assignment indicates a chaotic market for “used” cyberweapons. Initially tracked by a commercial monitoring service provider, the current wave of financial attacks is attributed to UNC6691, a financially motivated threat actor based in China. This group appears to have acquired the full exploit kit after it was previously used by UNC6353, a suspected Russian spy group targeting Ukrainian infrastructure in mid-2025.
The shift from espionage to theft suggests that once a zero-day vulnerability appears, its commodification is inevitable. UNC6691 deployed the kit on a large scale, moving away from the precise targeting of its Russian predecessors to a “cast-wide net” approach suitable for an iPhone cryptography exploit. This democratization of advanced scams significantly complicates the defense landscape, as tools designed to circumvent government-level security are now being trained on retail crypto investors.
EXPLORE: Best New Cryptocurrencies in 2026 – Watchlist of Recently Launched Coins and Investments
iPhone users holding crypto: are you at risk?
The specific profile of victims of this campaign is surprisingly small but very vulnerable: iPhone users who have failed to update their devices after iOS 17.2.1 and who engage in high-risk browsing behaviors. If you’re using an older device to trade on obscure decentralized exchanges or visit gray market gambling sites, you’re essentially walking through a minefield. The most critical defensive step is to immediately update to the latest version of iOS, as the Coruna exploit relies on vulnerabilities already patched by Apple.
For users unable to update their hardware, enabling Apple Lockdown Mode provides a strong defense against this specific iOS vulnerability. It restricts complex web technologies such as JavaScript Just-in-Time (JIT) compilation, which the exploit relies on to execute its code. Additionally, serious investors should consider their mobile devices compromised.
Never store seed phrases in screenshots or notes apps, and consider using a hardware wallet that requires physical confirmation for transactions. It’s simple: if your phone can be compromised by visiting a website, your hot wallet is not safe; It’s a donation box. Stay vigilant.
DISCOVER: What is the next crypto to explode in 2026?
following
Disclaimer: Coinspeaker is committed to providing unbiased and transparent reporting. This article is intended to provide accurate and current information, but should not be considered financial or investment advice. Because market conditions can change quickly, we encourage you to verify the information for yourself and consult a professional before making any decisions based on this content.

Daniel Frances is a technical writer and Web3 educator specializing in macroeconomics and DeFi mechanics. Hailing from crypto since 2017, Daniel leverages his experience in on-chain analytics to write evidence-based reports and in-depth guides. He holds certifications from the Blockchain Council and is dedicated to providing “insight gain” that overcomes market hype to find real utility for blockchain.