A man answered her door expecting a package. What happened instead was a crew of thieves posing as pizza delivery men who tied him up with duct tape, beat him with a gun, threatened to cut off his fingers, and made off with $13 million in cryptocurrency. The whole flight lasted about an hour.
This attack, which occurred on November 22 in the Mission Dolores neighborhood of San Francisco, was not an isolated incident. At least three related attempts followed in Sunnyvale, San Jose and Los Angeles in the weeks since, and they share a method that no password manager or two-factor authentication can stop.
The Model: Why Crypto Wealth Makes You a Physical Target
These crimes have a name in security circles: $5 attacks. The term, originally coined in a 2011 webcomic, captures the basic logic. If a criminal can’t crack your encryption, they are completely unaware of the technical problem and put pressure on you directly. The tool is not sophisticated. The lever is your security.
Security consultant Ordekian made it clear: an author who lacks the technical expertise to hack a crypto wallet can resort to cruder methods. This observation is no longer theoretical. This is a folder.
The San Francisco victim lost $10 million in Bitcoin and $3 million in Ethereum in a single forced transfer. Since cryptocurrency transactions are irreversible by design, there are no anti-fraud services to call, no chargebacks to file, and no grace period. Once the seed phrase leaves your control, the funds are gone. Think of it as a safe bolted to your floor, except the combination is stored in your head, meaning the safe is as secure as you are.
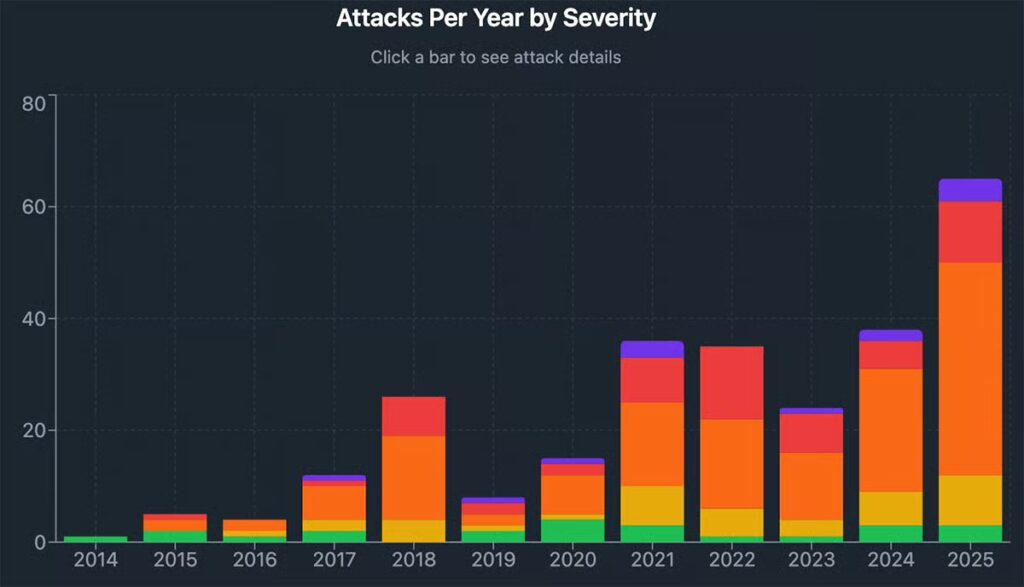
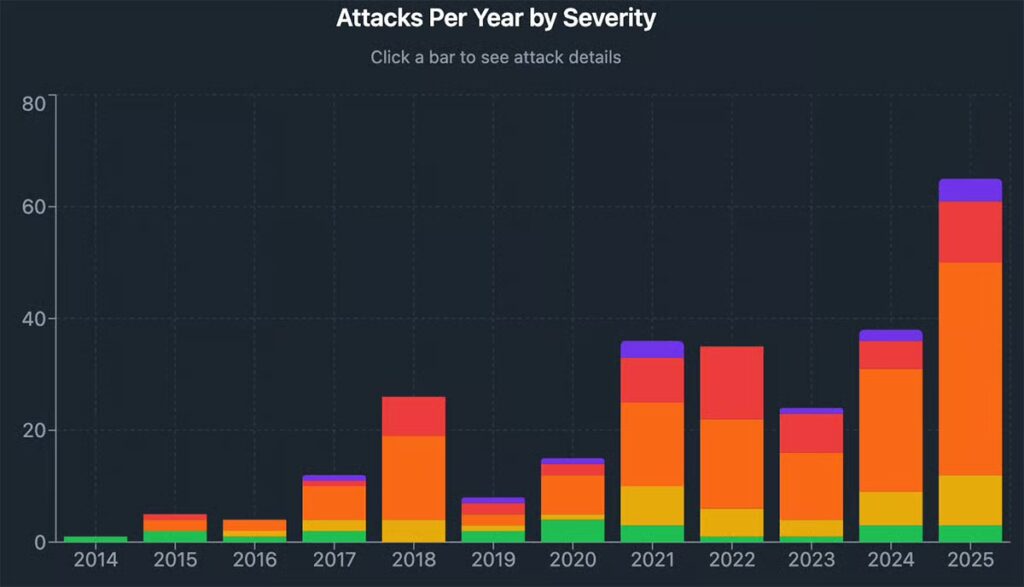
This vulnerability is not new, but it is accelerating. Violent cryptocurrency kidnappings have also been documented across Europe, with French organized crime unit SIRASCO tracking dozens of cases involving physical coercion of cryptocurrency holders. The recent California wave is part of a trend taking shape globally as the asset class grows and wealth becomes more visible.
If you hold any significant crypto, someone somewhere may already be looking for you. Whether they can find you is another question.
The mechanism: how attackers identify their targets
The timeline of the San Jose victim deserves careful study. Two unsolicited pizza deliveries arrived eleven days before the attack. Two days before the attack, strangers offered to pressure wash her driveway for free. The same day, an armed suspect was waiting in his driveway. This is not due to chance. It’s recognition.
In several Bay Area cases, investigators believe suspects infiltrated victims’ DoorDash or Uber Eats delivery accounts to obtain their home addresses. A username linked to a crypto forum or exchange account is often enough to connect a digital identity to a physical location, especially when that same username appears in public transaction records, Discord servers, or social media profiles showing wallet screenshots.
The Los Angeles cases revealed an additional vector: young crypto holders, sometimes called “crypto kids,” who have accumulated significant sums and made their wealth visible on platforms like Instagram.
A former LAPD officer, Eric Halem, was convicted in March 2026 of robbing a 17-year-old who arrived in the city with a hard drive containing $350,000 in stolen Bitcoin. The public display of wealth made target selection very easy.
Blockchain data is public by default. If your wallet address has already appeared in a forum post, in a screenshot of a tax document, or on a social network, someone with modest research skills can estimate your holdings without hacking anything. You basically live in a glass house and some people now come through with cards.
Follow 99Bitcoins on X and subscribe to YouTube for ongoing coverage of crypto security.
The article Violent Crypto Robberies Rise in Los Angeles and Bay Area appeared first on 99Bitcoins.