The Irish crypto wallet was supposed to be a digital tomb. For ten years, 500 Bitcoins remained intact, locked behind a cryptographic wall that everyone believed to be impenetrable.
This hypothesis ended on Tuesday.
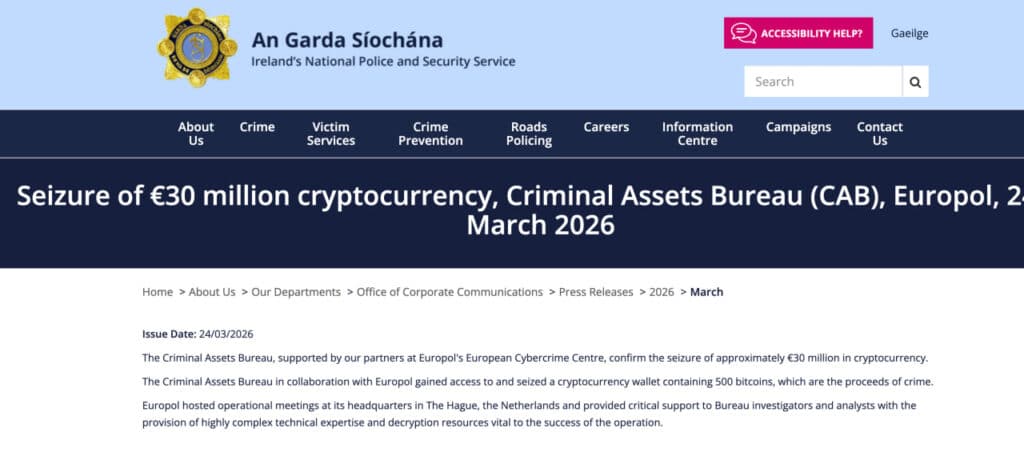
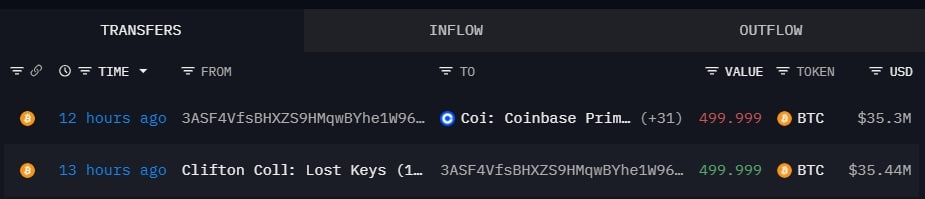
In a move that stunned on-chain analysts, the Criminal Assets Bureau (CAB) in Ireland managed to transfer $35 million worth of BTC from a wallet linked to drug trafficker Clifton Collins. The funds were sent to Coinbase Prime, signaling a state-controlled liquidation. This is not just a salary for the Irish Treasury. This proves that “lost” keys are not always as lost as we think.
The impossible has happened. And the privacy implications of cryptocurrencies are enormous.
The issues: when “irrecoverable” is not
For years, the crypto industry has operated by a binary rule: if you don’t have the private keys, the money effectively doesn’t exist. He is burned. Disappeared.
This BTC seizure calls this absolute into question.
Clifton Collins claimed his keys were physically destroyed. The crypto community believed the assets had been frozen in time, much like the millions lost in other high-profile cases where security measures became obstacles to recovery. We treated these coins as permanently removed from circulation.
But on-chain reality disagrees. If law enforcement can resurrect dormant parts after a decade, the definition of “inaccessible” needs to be updated. The barrier between a locked wallet and state seizure is thinner than you think.
The operation: how they probably solved it
How can the police break into a Bitcoin wallet without the password? They generally don’t break Bitcoin itself. They break the user.
The cryptographic hash function used to secure the Bitcoin network (SHA-256) is unbreakable. You can’t brute force a private key: it would take more energy than there is in the sun to guess it. But Europol and the CAB did not need to break the math.
500 BTC out of 6,000 BTC owned by drug dealer Clifton Collins was moved after 10 years and sent to Coinbase Exchange.
The keys were kept on a fishing rod at a rental house, which were then sent to a landfill in 2017 after his arrest.
I guess the keys were never lost ;)… pic.twitter.com/zEHNoS62oD
—Sani | TimechainIndex.com (@SaniExp) March 24, 2026
Think of a Bitcoin wallet as a titanium safe. You can’t drill through metal. But if the owner wrote the combination on a post-it note in a nearby locked desk drawer, you don’t need to drill into the safe. All you have to do is pick the office lock.
In Blockchain Forensics cases, investigators look for these “desk drawers.” This often means finding a digital file, such as a wallet.dat file – on a computer entered. These files contain the keys but are often protected by a weaker, human-created password.
With the help of Europol’s cybercrime center, Irish police likely used massive computing power to guess thousands of password combinations from a seized file. Or maybe they grabbed a fragment of a seed phrase from a cloud backup or old hard drive.
It’s a method we’re seeing escalating globally, similar to how the United States tracks and seizes assets from sophisticated state actors. The chain is transparent; if you leave a single digital footprint leading to your keys, these agencies will find it.
The titanium safe held up. Human security around this situation has failed.
The case: a fishing rod and a $370 million mistake
Clifton Collins’ story reads like a tragic comedy of errors.
A former beekeeper turned cannabis grower, Collins was an early adopter. He bought Bitcoin in 2011 and 2012 when the price was negligible, using money from his crop sales. In 2017, he had amassed 6,000 BTC.
(Source: Arkham)
Paranoid about security, Collins allegedly printed his private keys on a piece of paper. He hid this paper in the cap of a fishing rod case in his rented house in County Galway. It was the ultimate “cold storage.”
Then came the arrest. While Collins was serving a five-year sentence for drug offenses, his landlord hired professional cleaners to empty the house. The fishing rod case and codes for a fortune were thrown into a landfill.
At least that’s what the story goes.
As of 2020, the CAB was ready to seize the assets, but the “lost keys” narrative held them back. The wallet affected in this week’s operation was labeled “Clifton Collins: Lost Keys” by analytics firm Arkham Intelligence. It was one of 12 portfolios containing his total fortune.
The movement of these 500 BTC suggests that either the fishing rod story was a fabrication, or Collins had a backup that he didn’t mention. The police found an entrance door. We are witnessing the slow dismantling of a perfect crime.
What it proves: the forensic threshold
This operation is a signal. State level capabilities Blockchain forensic analysis have crossed a threshold.
Ten years ago, a criminal could reasonably expect that a laptop seized with a crypto wallet would be safe. The police had the equipment, but not the sophistication to bypass layers of encryption. Those days are over.
Agencies like CAB, supported by Europol, now have the tools to hack into what criminals thought was definitively secure. We’ve seen this trend accelerate in the United States with lawsuits against figures who thought they could hide behind the technology.
The main argument in favor of this development is justice. Proceeds of crime are recovered; victims or taxpayers benefit. The bear’s case is privacy. If the state can hack a drug dealer’s “lost” wallet, the tools exist to hack others.
Monitor the remaining 11 wallets. If CAB moves the rest of the 5,500 BTC, we will know for sure that the “lost keys” defense is completely dead.
The post Cracked: How Irish Crypto Authorities Finally Moved 500 “Inaccessible” Bitcoins appeared first on 99Bitcoins.