Key points to remember:
- Project Eleven awarded researcher Giancarlo Lelli 1 BTC ($78,000) for hacking a 15-bit ECC key on IBM quantum hardware on April 24.
- Bitcoin the developers showed that Lelli’s results replicated with random noise, signaling zero quantum advantage over classical methods.
- The 15-bit gap at BitcoinThe 256-bit secp256k1 remains a technical chasm of 2^241, leaving BTC security intact for the moment.
Project Eleven Hands Giancarlo Lelli 1 BTC for 15-bit ECC Quantum Break, but software developers call it noise
Project Eleven described this exploit as a 512-fold increase in search space complexity compared to a previous 6-bit ECC break performed by engineer Steve Tippeconnic on IBM hardware in September 2025. CEO Alex Pruden presented the exploit as proof that quantum attacks on ECC no longer require national labs or proprietary hardware.
The award, worth approximately $78,000 at time of award, was designed to provide reproducible public measurements of quantum attacks on ECC for key sizes between 1 and 25 bits. Lelli’s submission, including the full code and execution logs, is publicly available on Github.
Lelli implemented a two-register variant of Shor’s algorithm on IBM Quantum cloud hardware, targeting elliptic curves of the form used in Bitcoinof the secp256k1 standard. The circuit ran on several IBM Heron r2 processors, including ibm_torino and ibm_fez, and relied on techniques designed for noisy intermediate-scale quantum devices.
Bitcoin developers and cryptographers quickly dismissed the result, saying the quantum hardware added no significant value to the result. The Project Eleven post
Ancient Bitcoin Senior maintainer Jonas Schnelli analyzed Lelli’s submission and found that the IBM circuit, running about 98,000 gates with about 99.5 percent fidelity per gate, produced outputs that were statistically indistinguishable from random coin flips.
Schnelli reproduced the complete key recovery in about 20 lines of Python using purely random bits, with no quantum hardware involved. His conclusion was straightforward: the quantum computer added no detectable signal compared to classical chance.
Coinkite founder Rodolfo Novak has insisted that Project Eleven is misleading the public, calling its quantum claims “theater.” On private key is classically solved before the quantum circuit even works” and the system “finds nothing – we tell it the answer”, adding that the results rely on “a classical verification filter”. Novak concluded that even if “the quantum threat to Bitcoin is real but distant”, today’s demos are “classical calculations dressed in quantum costumes”.
Researcher Yuval Adam independently confirmed this finding by replacing Lelli’s IBM quantum backend with /dev/urandom, Linux’s classic random number generator, and retrieving the target key identically. The 15-bit curve has a search space of only 32,767 possible private keyssmall enough that a typical verifier checking candidates against the public key would find a match through quasi-random sampling with high probability.
Bitcoin Proponent Jimmy Song described the quantum computer as serving the same function as /dev/urandom. The TFTC
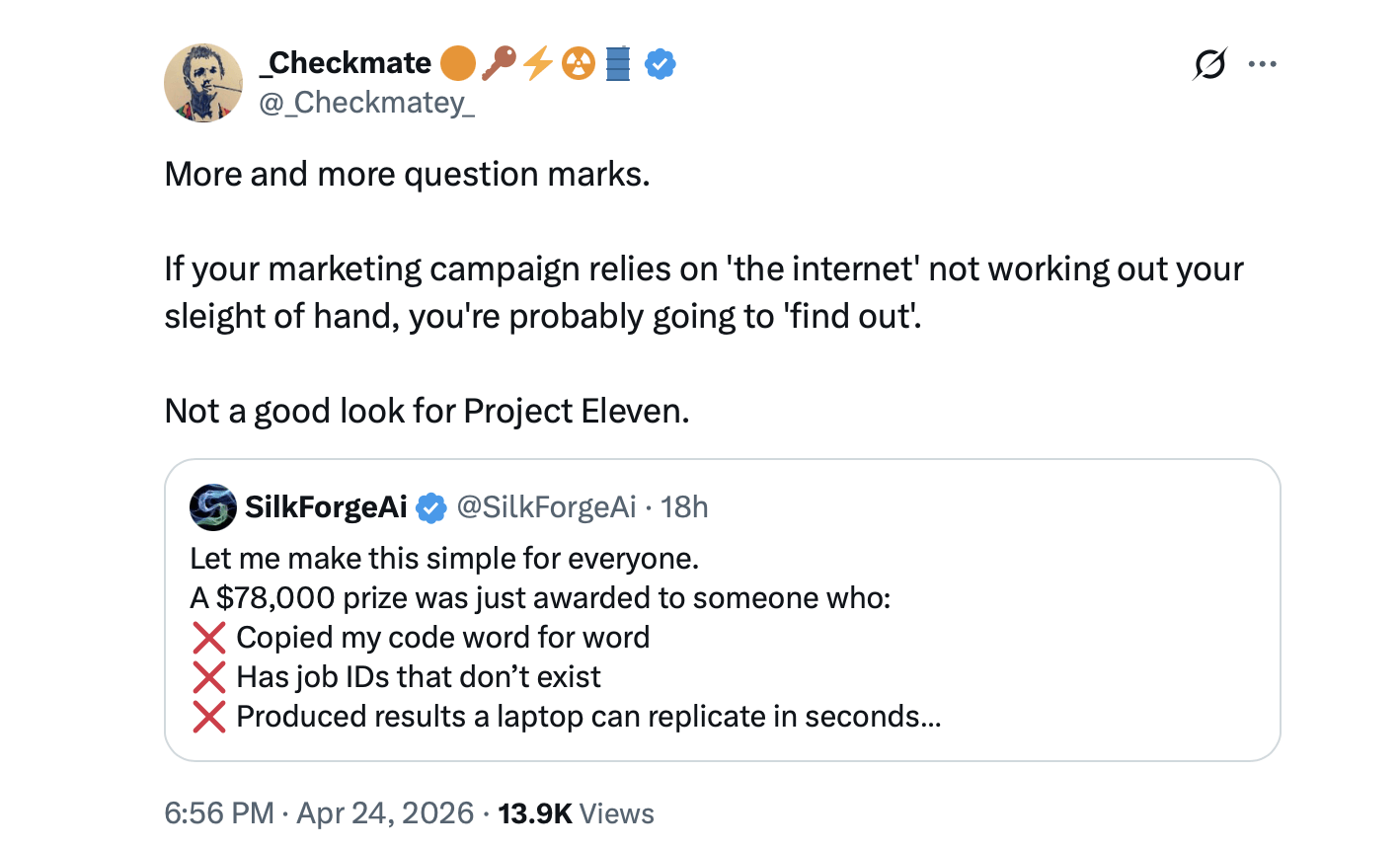
Critics have also pointed to a conflict of interest in the pricing structure. Project Eleven, backed by Coinbase Ventures, Castle Island Ventures, Variant, and Balaji Srinivasan, created the prize, evaluated applications by three independent physicists, awarded the bounty, and then issued press releases warning that approximately 6.9 million BTC held in wallets with exposed public keys faced potential long-term risk. The company sells post-quantum cryptography tools.
Project Eleven founder responds to criticism
Pruden acknowledged in a subsequent thread that the outcome was not Q-Day and that NISQ-era experiments routinely depended on classical attendance. He argued that the demonstration still represented incremental, repeatable progress on publicly accessible hardware and that planning for migration to post-quantum cryptography remained a reasonable long-term priority. The Project Eleven leader added:
“Bottom line: This is incremental progress in an early, noisy area – not Q-Day. It highlights why we’re tracking resource reductions and why post-quantum migration planning is important for long-term security. Skepticism is healthy; moving the goalposts is not. Happy to discuss technical details or share repo/judge feedback.”
The gap between Lelli’s result and any practical threat to Bitcoin is considerable. Bitcoin’s secp256k1 curve works with 256-bit security. The distance from 15 bits to 256 bits represents a factor of 2 to the power of 241 in computational difficulty. Even recent, optimistic research, including a Google paper published in April 2026, estimates that breaking 256-bit ECC would require fewer than 500,000 physical qubits, a threshold that current quantum hardware falls well short of.
The episode illustrates a tension that persists in coverage of quantum computing: Incremental hardware steps grab the headlines, but the distance between toy-scale demonstrations and production cryptographic systems remains a technical gap with no near-term solution. Bitcoin’s security model depends on this loophole, and developers say it remains intact.